Hello friends–recently I am hosting a live capture the flag event for penetration testing / hacking methodology practice. You can find the post here: REDTEAM CTF CHALLENGE
While chatting with one of the participants, I decided to rack up a few points from the malicious attack category (though I assure you what I did was harmless. . . mostly!). First I had to get him interested enough in knowing me to talk. Now I will discuss how Social Engineering can be employed with a low level of technology to make an effective attack.
I demonstrated value by discussing that I was a DJ and provided a link to this page: DJ_Mission – Mixcloud
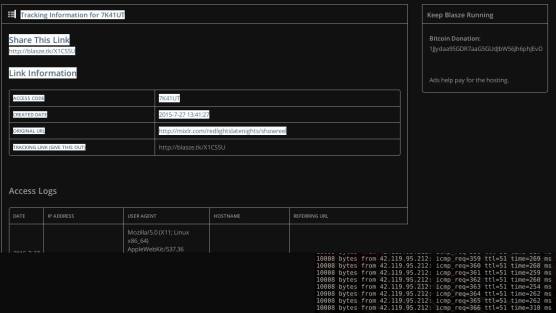
However the page was put through a redirect site which takes the clicker’s IP address in a log dump and makes it available to you through the front end. No programming required! The page I used to generate the redirect link was blasze.com and the way you do it is pick a page you want to send them to, enter the url and blamm-o! It spits out the link you need to give to them.
But wait! That blasze.com link looks too suspicious, so what you do is use the google shortener to obfuscate. This is beginning the chain on your attack. Hide your url w/ goo.gl!
Then. . . I sent him the link and waited like a hungry spider hacker inside my cyber web I constructed to lure the perfect victim.
It took 20 seconds to get the Vietnamese IP address.
This is a screen from the dump page. I don’t like white screens so I use the Blank Your Monitor for firefox so my internets looks cool like that.
NEXT once I had the IP address I used a script in my Kali Linux terminal to begin the final phase of my two-hit combo chained cyber attack on Facebook friend! I used a script that looked like:
ping -var 65535 xxx.xxx.IP.address
This began a ping flood that can smash the stack on the network, bringing civilization as we know it to a grinding halt. But in all reality, it was only a minor annoyance =)
Thanks for reading!

Reblogged this on Briq Haus Ltd. Security & Intelligence and commented:
This is an old post I dug up for the sake of building more security blog entries.
LikeLike